So today I come up with the operating systems that hackers used for
hacking. The top on this list is the Kali Linux which has almost all
type of hacking tools that are totally free for everyone. All operating
systems are based on Linux kernel, we know the reason behind this fact,
that Linux is free and open source.
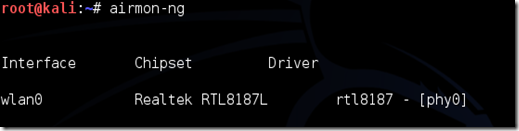
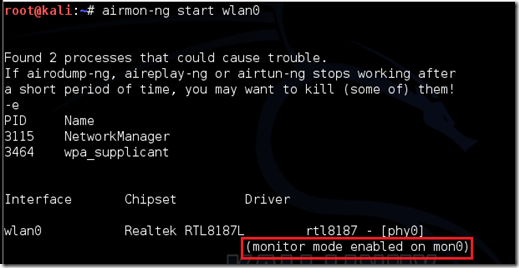
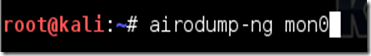
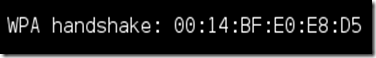
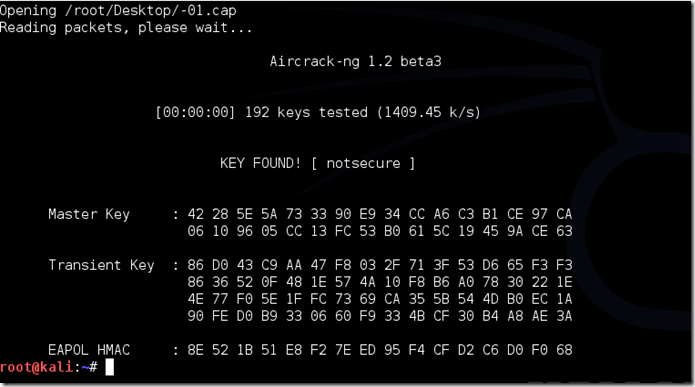
Kali Linux
Kali Linux comes from the creators of BackTrack Yes you guessed it they are Offensive Security
team. Kali Linux is the most versatile and advanced penetration testing
distro. Kali Linux updates its tools, and it is available for many
different platforms like VMware, ARM, and many more, one of my favorite
is Kali Linux on Raspberry Pi. You can find all over here.

BackBox
BackBox is a Linux distribution based on Ubuntu. It has been developed
to perform penetration tests and security assessments. BackBox is
lightweight OS and requires less hardware specification. Designed to be
fast, easy to use and provide a minimal yet complete desktop
environment, thanks to its own software repositories, always being
updated to the latest stable version of the most used and best known
ethical hacking tools.
DEFT
DEFT Association is an non-profit association. They provide a reliable
and powerful Penetration testing distribution of Linux. You can download
DEFT ISO or VMware virtual machine image from their official website.
Live Hacking OS
Live Hacking OS is also based on Linux, you know why. It is also a big
pack of hacking tools used for Penetration testing. It includes the
graphical user interface GNOME inbuilt. There is a second variation
available which is command line only. And requires very less hardware
requirement.
Samurai Web Security Framework
The Samurai Web Testing Framework is a live linux distro which is
pre-configured with Web penetration testing tools. Yes this is the best
for Web Penetration Testing and this is a live linux which is beneficial
to clear all hacking tracks. You can download VMware image as well as
ISO image from Sourceforge.
Network Security Tool Kit
Network security toolkit is based on Fedora and runs on 32 as well as 64
bit platforms. Network security toolkit provides tools to test, monitor
and fix the network issues. The main purpose of developing this Toolkit
is to provide the security professional and network administrator with a
comprehensive set of Open Source Network Security Tools.
Parrot Security OS is a cloud friendly operating system designed for
Pentesting, Computer Forensic, Reverse engineering, Hacking, Cloud
pentesting, privacy/anonimity and cryptography. Parrot security os is
based on Debian and developed by Frozenbox network. Parrot-sec is available in 32 bit for Intel processors and 64 bit for AMD.
Bugtraq
Bugtraq Team is experienced freaks and developers. Bugtraq is available
in Debian, Ubuntu, OpenSuSe in 32 and 64 bit architectures. Bugtraq
system offers the most comprehensive distribution, optimal, and stable
with automated services manager in real time. This distribution based on
the 3.2 and 3.4 kernel.
Nodezero
Nodezero is very handy Penetration testing tools collection distro. They
believe that Livecd is not for those who does Penetration testing on
regular basis, but they provide livecd of their distro. Nodezero is
reliable and stable. It is based on the Ubuntu distribution of Linux.
Download your free and open copy of NodeZero Linux today, because real
hackers count from zero.
Pentoo
Pentoo is a security-focused Linux distro based on Gentoo. It is
basically a Gentoo install with lots of customized tools, customized
kernel, and more. Here is a list of the features currently included :
- Hardened Kernel with aufs patches
- Backported Wifi stack from latest stable kernel release
- Module loading support ala slax
- Changes saving on usb stick
- XFCE4 wm
- Cuda/OPENCL cracking support with development tools
- System updates if you got it finally installed
GnackTrack
GnackTrack author is no longer updating its distro since the release of
BackTrack5. GnackTrack is similar OS as BackTrack with the
implementation of Gnome.